Are you tired of clicking “Allow” multiple times or everytime you are trying to access your PowerApps App? Well, worry not. PowerShell Administration module for PowerApps is here with a commandlet to ease your life. Let’s take a look.
Problem Statement
While accessing our PowerApps apps we see the below message and we have to allow all the connections which can at time be very furstrating.

Some times we even need to click allow multiple times for certain connections.
Solution
With the help of the the PS module Microsoft.PowerApps.Administration.PowerShell (link to download/install the module), and a specific cmdlet Set-AdminPowerAppApisToBypassConsent, we can now by pass an app from asking this consent from the user.
What we need to do:
- Goto make.powerapps.com.
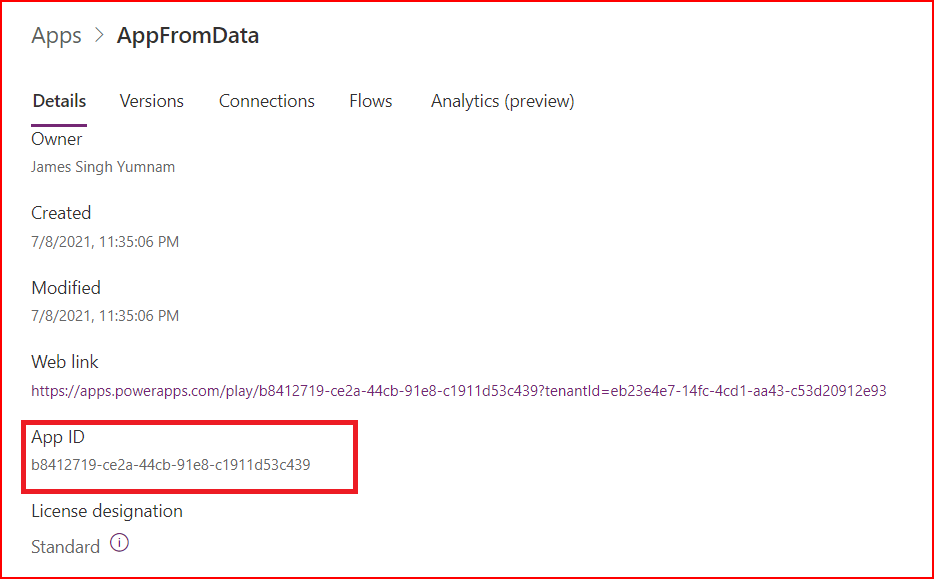
- Under Apps, open the context menu using the ellipse for the partciular app you want to bypass the consent prompt and open details.

- Copy the App ID and note it down. (We need this ID later to use with the cmdlet)
- Open PowerShell Console or you can even you Visual Studio Code. (I will use PowerShell Console for this simple command) and Install the PS module Microsoft.PowerApps.Administration.PowerShell. Follow the installation steps as mentioned in the Microsoft Docs here.
- After successful installation, write the below command:
Set-AdminPowerAppApisToBypassConsent -AppName b8412719-ce2a-44cb-91e8-c1911d53c439
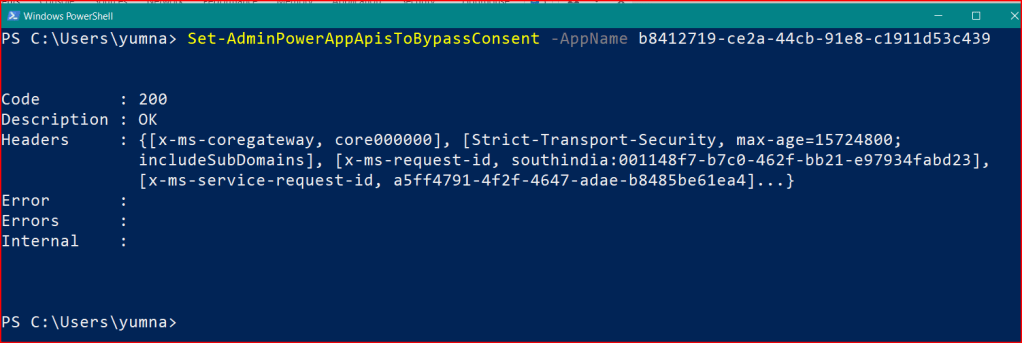
Note: When prompted to sign in to your M365 account, complete the sign in process.
Now, when I open the app again or refresh the page where consent prompt is displayed, it will directly open the app for me even though I have not clicked on the Allow button.
Bypass consent cmdlet In Action

ByPass API Consent
This will be applied to all the users. It means that when any user accesses the app, they won’t have to face this challenge.
Bonus
This could lead to a compliance issue. So, if you want to again enable the same consent prompt for this particular app, run the below command in PS console.
Clear-AdminPowerAppApisToBypassConsent -AppName b8412719-ce2a-44cb-91e8-c1911d53c439

Thank you for being till here. See you in the next blog.


Leave a comment